A serious Bash vulnerability has been discovered on Wednesday (first public mention of it seems to be this post on seclist continuing here with more details). This allows an attacker to execute any code on a vulnerable server. This is even more serious than the heartbleed vulnerability that swept through the Internet couple of months ago.
This is not a WordPress vulnerability, but a server vulnerability. It threatens to become one of the most widespread and dangerous exploits with serious security implications (it received both Impact and Exploitability scores of 10/10). If you have a server, own/manage websites or use a Mac – read on.
Do you have vulnerable bash?
There are several ways you can test.
(Update: ManageWP WordPress plugin and ManageWP code snippet now test for both disclosed shellshock vulnerabilities CVE-2014-6271 and CVE-2014-7169 )
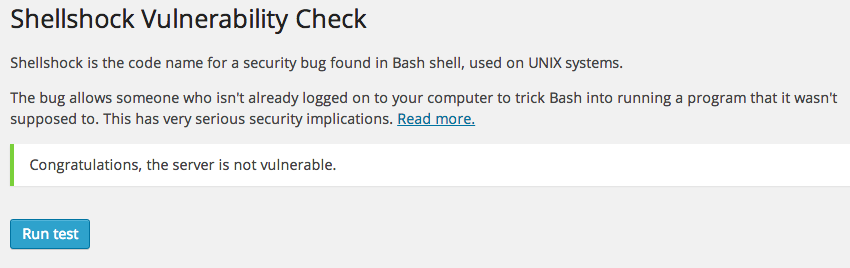
1. Use Shellshock check WordPress plugin
ManageWP released a WordPress plugin that checks if your server has vulnerable version of bash installed.
Download Shellshock check WordPress plugin
To use it, just install the plugin and click Run test.
2. With ManageWP
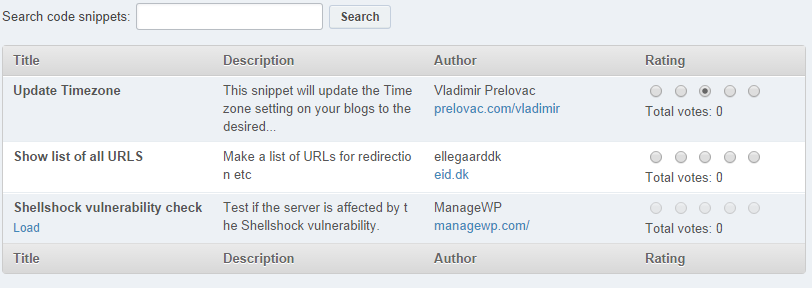
If you own/manage multiple sites, we have published a code snippet which allows you to check all your websites with a click of the button.
Access it through Tools -> Code Snippets (available to Professional and Business plan users, as well as trial users). Scroll to public snippets and locate ‘Shellshock vulnerability check’ then click Load.
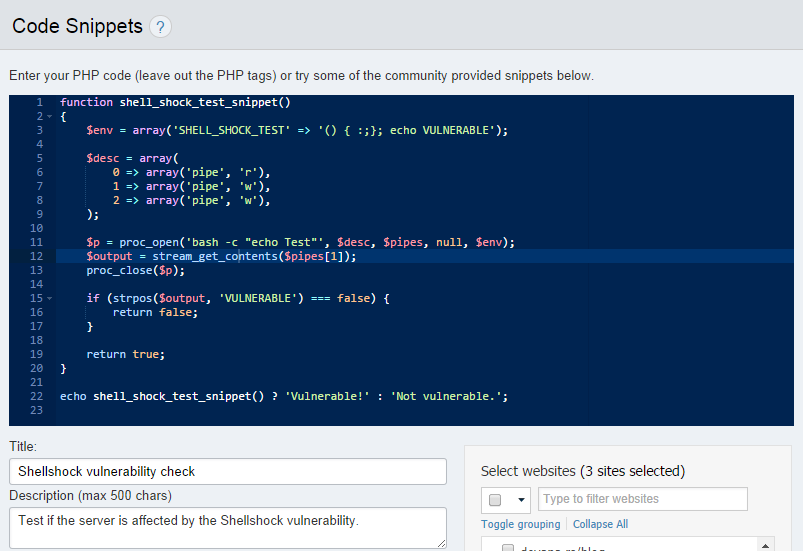
This is what the snippet looks like.
Select sites you want to check for vulnerability and click Execute. You will get a response that will look like this.
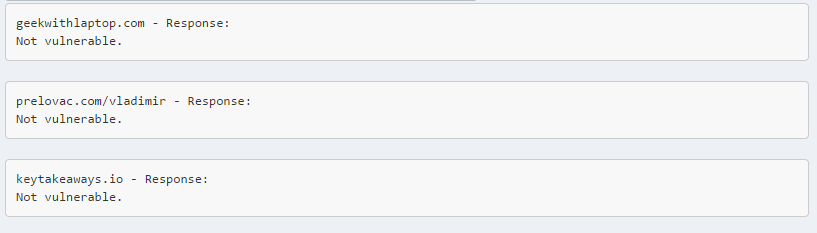
Note that if a server is vulnerable, all sites on the server will report vulnerability.
3. If you have admin access to your server
If you have shell access to your server you can run this code.
env x='() { :;}; echo VULNERABLE' bash -c 'echo hello'
If you see the string VULNERABLE in the output your bash is vulnerable.
How does Shellshock work?
This is the official explanation on NIST:
GNU Bash through 4.3 processes trailing strings after function definitions in the values of environment variables, which allows remote attackers to execute arbitrary code via a crafted environment, as demonstrated by vectors involving the ForceCommand feature in OpenSSH sshd, the mod_cgi and mod_cgid modules in the Apache HTTP Server, scripts executed by unspecified DHCP clients, and other situations in which setting the environment occurs across a privilege boundary from Bash execution.
Specific examples of how to use the exploit are already plentiful and include scripts that detect vulnerable servers and access the password file, basically possibilities are endless.
What can you do?
If you have access to your server simply update bash via
yum update bash
or
apt-get install --only-upgrade bash
If you do not have access then you need to contact your server/hosting support and point them to this post, they will know what to do.
Shellshock also affects Macs. Useful information for Mac users can be found here.
For more detailed analysis of the exploit see here.
We will follow the proceedings of the event and update you with the most important information accordingly.
Leave a Reply