Despite being the most popular content management system to date, WordPress is still vulnerable to security breaches. In fact, we have mentioned before that there are nearly 4,000 known WordPress vulnerabilities in existence, threatening to destroy the hard work you have put into your website.
There are many entry points that can compromise your website and all of its data. For example, hackers can sneak in through your themes, via password theft, with brute force attacks, and even using old files.
And, with 61.5% of WordPress users admitting they don’t know how attackers get into their website, this should call for more education about website vulnerabilities.
More specifically, we should focus on the one thing that makes your website the most vulnerable – plugins.
Today we are going to look at how and why hackers might try to break into your website, and what you can do to prevent this from happening, so that you don’t become a victim to a plugin exploit and risk losing everything you worked so hard to achieve.
Why do hackers want into your WordPress website?
To start, it is important to understand that despite your best efforts to keep your WordPress website safe, plugins expose your website to a variety of security breaches.
This is because, although the WordPress core is safe and secure, plugins come from all over the place, are developed by tons of different people with different skill levels and standards, and quite frankly, are wildcards that you simply throw into your website.
And, if you are not careful, these wildcards have the potential to do a lot of damage.
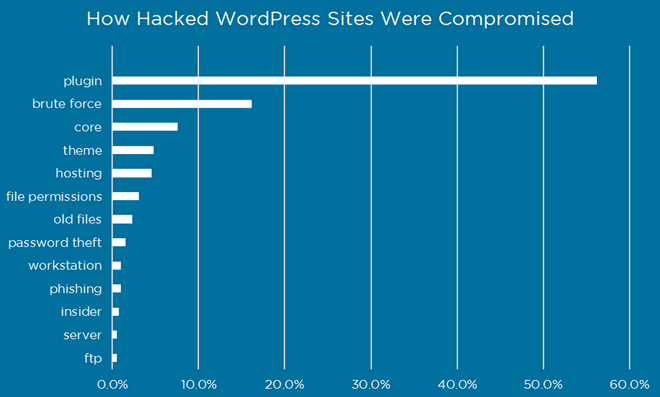
According to research conducted by Wordfence, plugins are the root cause of most WordPress website hacks because hackers know how to exploit the fact that not all WordPress plugins are secure.
In fact, plugins account for nearly 60% of all WordPress breaches, meaning they have the potential to be your biggest security enemy.
Take a look at some of the most common ways hackers take advantage of your plugin vulnerabilities:
- Placing links on your site in an effort to boost their own site’s SEO
- Installing malicious code onto your site
- Redirecting your site visitors to other sites rather than staying on yours
- Using your server resources for things like spam email and DDoS attacks
As you can see, there are several ways a hacker can break into your website, especially using your site’s plugins. However, there are several ways you can prevent plugin vulnerabilities (and security breaches) on your website.
How to address plugin vulnerabilities on your WordPress website
Here are some of the most efficient and proactive things you can do to protect your WordPress website from plugin vulnerabilities.
1. Use a security plugin
In the past, we have shared with you some of the very best WordPress security plugins available to WordPress users. And, though your website’s security plugin will not be able to stop all hackers from getting in, it’s always a good idea to have a solid security plugin installed on your website to help prevent any attacks.
There are plenty of options for you to choose from and they all have their own unique set of features. So, check out the reliable options and make a decision that best suits your security needs.
2. WPSCan vulnerability database
If you check out the WPScan Vulnerability Database, you will be able to see an entire list of plugins posing security threats to those with WordPress websites. More so, you can search by plugin name to see if a particular one has made the list, or simply search the list in alphabetical order.
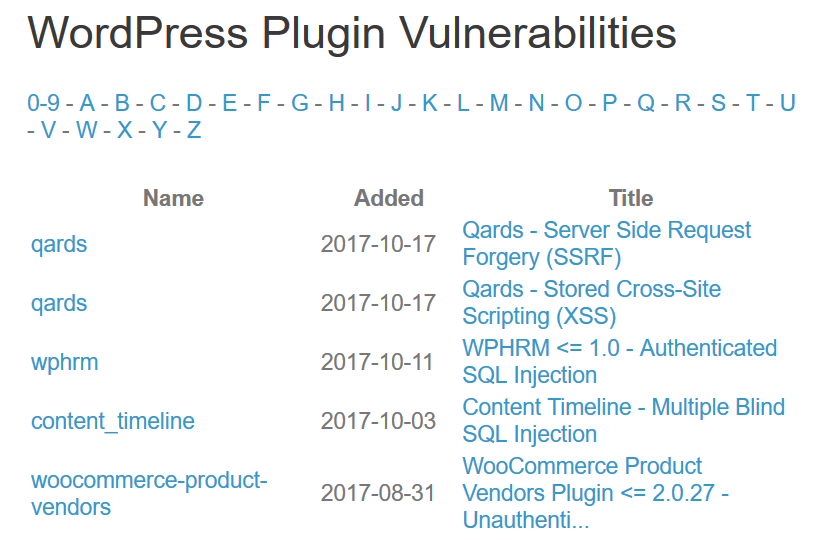
If you notice a plugin that you use is on the list, make sure there is no update resolving the vulnerability before taking action.
If no solution has been applied, you might want to delete that plugin from your website and find an alternative that doesn’t open your site up to hackers.
3. Use ManageWP vulnerability updates
ManageWP is dedicated to protecting your WordPress website from all security breaches. That’s why they brought you an advanced way of checking for plugin vulnerabilities on your website when you use ManageWP’s website management services.
This Vulnerability Update feature, available free of charge to all ManageWP customers, not only informs you when a plugin on your website has become vulnerable, but explains what the exact issue is, and where on your website this plugin is working so you can see what kind of an effect deleting it may have.
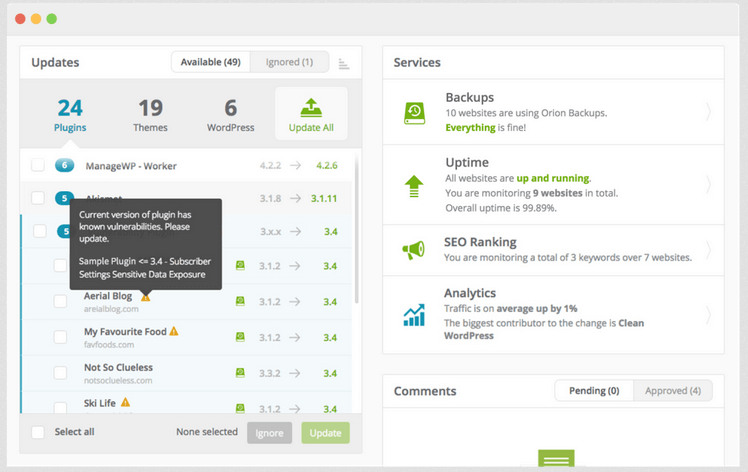
In addition, if you hover over a known plugin vulnerability, you will notice a vulnerability fix so that resolving the issue becomes even easier.
4. Take care of your plugins
There is a lot more to caring for your WordPress website’s security than installing a security plugin and hoping for the best. In fact, many plugin vulnerability issues can be avoided with a little extra TLC from the beginning.
Take a look at how to care for your plugins so you can prevent security breaches and protect your website from hackers:
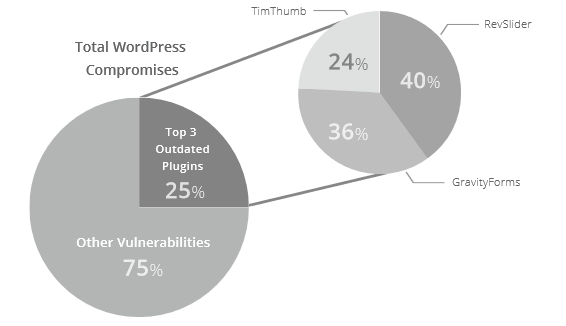
- Update Your Plugins. Always make sure your website’s plugins are updated. Updates typically improve the plugin and patch possible security issues, both of which you want to take advantage of. Check out Sucuri’s analysis of outdated plugins. Three plugins (even the popular Gravity Forms) account for 25% of all WordPress website compromises. Don’t let an outdated plugin make your site vulnerable.
- Reputable Developers. Choose plugins form reputable marketplaces such as the WordPress Repository (where all plugins undergo strict screening processes), CodeCanyon, and third-party developers you trust. Check for things like user ratings and reviews, updates and compatibility, support, documentation, and active installations to ensure they are secure for use on your website.
- Avoid Abandoned Plugins. This falls in line with always updating your plugins. When a plugin is updated, this means that the developer of the plugin has screened the plugin for vulnerabilities and patched any issues. If you notice that a plugin you want to use on your website has not been updated in the past 6 months, consider using an alternative. Abandoned plugins are not actively being screened for security issues and expose your website to hackers.
- Delete Unused Plugins. Deactivating a plugin on your website and letting it sit untouched gives hackers the perfect opportunity to break in and use it to run malicious code on your website. If you don’t plan on using a plugin anymore, simply delete it.
In the end, performing these simple steps will help protect your hard work and maintain a seamless user experience for your site visitors.
Final thoughts
Plugins are great, don’t get me wrong. In fact, plugins are one of the main reasons the WordPress CMS is so popular. They extend the functionality and design of your website, oftentimes for free, and add a lot of value to your site visitors as they engage in your content.
However, failing to recognize the threat some plugins pose can do a lot of harm to your website. That’s why it is critical you conduct research before placing random plugins on your site, use reliable sources, and regularly monitor not only your website for changes that may lead to a breach in security, but other databases that will alert you to possible plugin vulnerabilities.
And, if you really want to make things easier, entrust ManageWP to manage and maintain your website, as well as keep it secure with advanced vulnerability scans.
Using the Orion Vulnerability Update feature, you can rest assured that your website is secure at all times. And, in the off chance it becomes vulnerable to attack, you can guarantee ManageWP will alert you immediately so that you can take the best measures to resolve the vulnerability and re-secure your website.

Leave a Reply